Retesting by hand costs you 3 hours per engagement
RiftX automates vulnerability retesting. Submit a finding, get a verified verdict with full evidence in five minutes, not thirty.
No credit card required. Set up in one session.
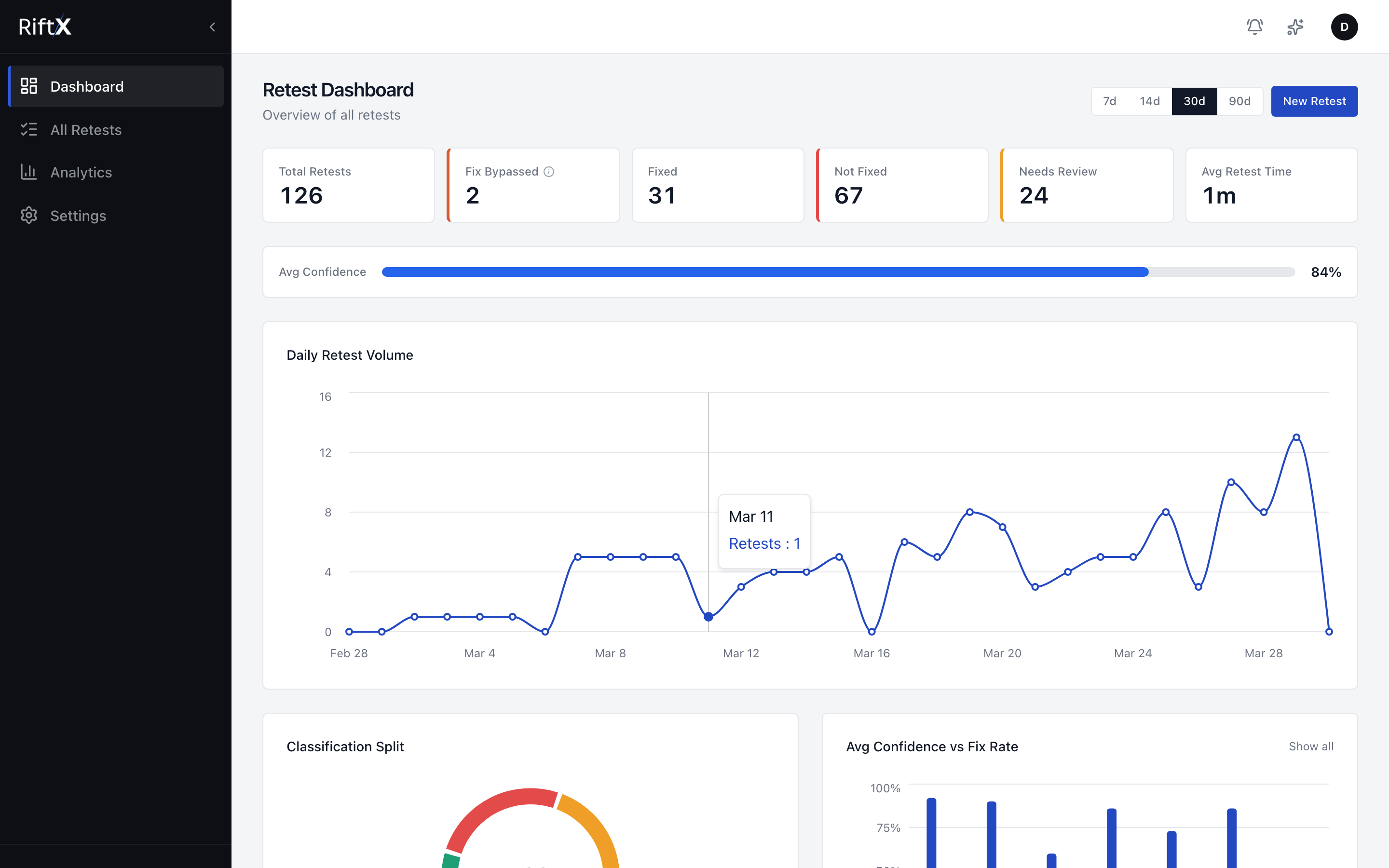
One screen to see every retest across every engagement your team is running.
Manual: 30 min. RiftX: 5 min.
CSRF, open redirects, clickjacking, and more
reproduction accuracy across regression tests
Real browser execution, not static analysis
Deterministic detection first, LLM fallback only
Evidence sealed with HMAC-SHA256
Every engagement, your team retests the same findings by hand. It costs more than you think.
That is not a pentester problem. That is a delivery capacity problem. Three hours per engagement spent on verification work that does not require human judgment.
Every engagement, the same loop: take a reported issue, reproduce it, capture proof, move on. RiftX compresses that loop without compromising the evidence your report depends on.
findings per engagement
suitable for RiftX
per finding
recovered per engagement
7-10 findings per engagement × 90% fit × 25 minutes saved per finding = 3 pentester-hours recovered per engagement.
Based on manual retest avg: 30 min. RiftX avg: 5 min. Time savings: 6x.
Manual retest avg: 30 min
RiftX avg: 5 min
Time savings: 6x faster
Internal benchmarks across regression test suite
How a 30-minute retest becomes a 5-minute verdict
Finding goes in. Verified verdict comes out. Your pentester moves on.
Submit Report
Via API or Dashboard
Provide the target URL and steps-to-reproduce. Payload is optional.
Agent Plans
Planning
Reads the reproduction steps, sets a clear verification goal, and plans how to follow it.
Browser Executes
Real Playwright Browser
An isolated browser follows your reproduction steps and fires signal detectors.
Evidence Delivered
HTTP traces, screen recording, confidence score
A verified verdict with full HTTP evidence and a screen recording, ready to include in your report.
Routine retest moving from report to verdict
Report queued
Plan selected
Browser executing
Evidence sealed
The finding types that eat your retesting time
From XSS and SQLi to CSRF, clickjacking, and open redirects. The common web findings your team retests every engagement.
XSS Retesting
Replays reflected, stored, and DOM XSS in a real browser. Submit steps-to-reproduce and get a verdict with dialog and DOM proof.
Fixed alert() intercepted
SQLi Verification
Verifies reported SQL injection findings and returns a clear verdict with response artifacts, not raw scanner output your pentester has to interpret.
500 syntax error observed
Web Misconfigurations
Verifies CORS, HSTS, CSP, and six more header categories. Returns report-ready evidence.
CORS ACAO:null + credentials allowed
IDOR Verification
Replays reported access control issues. Swaps the identifier, checks whether unauthorized data comes back, and returns the evidence.
403 → 200 unauthorized object returned
For the full technical detail on the agent loop, evidence model, and verdict logic, see the product page.
View Product DetailsHow the verification actually works
Deterministic signal detectors first, LLM fallback only when needed.
Built-in Safety Limits
If a limit is hit, the retest terminates rather than guessing. The system is opinionated about staying inside a safe verification boundary.
Evidence is part of the verdict, not an afterthought
Every verification produces a sealed bundle. Your pentester reviews evidence, not assertions.
<script>alert(document.domain)</script>- Navigate to https://app.target.com/search
- Enter payload <script>alert(document.domain)</script> in the search field
- Observe JavaScript execution via browser dialog interception
HMAC-SHA256: a3f2...8e91. Evidence integrity sealed
Full HTTP traces
Complete request and response for every step
Screen recording
GIF of the browser executing reproduction steps
Reproduction steps
Exact steps followed, ready for your report
Integrity seal
HMAC-SHA256 hash proving evidence was not modified
Built by someone who lived the retesting loop
After years of pentesting, I kept watching senior pentesters spend hours retesting the same reflected XSS they had seen dozens of times before. The loop was identical every engagement: navigate, inject, screenshot, write it up. I built RiftX because that loop should take five minutes, not thirty.
RiftX replays the path your pentester reported. It never generates its own attack surface.
Retesting is the part of the job that does not require human expertise. Everything else still does.
Signal detectors handle known patterns. The model is fallback, not foundation.
No client data used for model training · Isolated browser execution · Every action logged and auditable · Returns Needs Review when unsure, never guesses
Currently in private beta. Onboarding consultancies with repeatable web retesting workflows.
Get your pentesters out of the retesting loop
Your pentesters should be finding vulnerabilities and writing reports, not manually retesting the same XSS for the third time this month.