See how a 30-minute retest becomes a 5-minute verdict
Submit a reported web finding with reproduction steps. RiftX turns a 30-minute manual retest into a verified verdict with full HTTP evidence in five minutes.
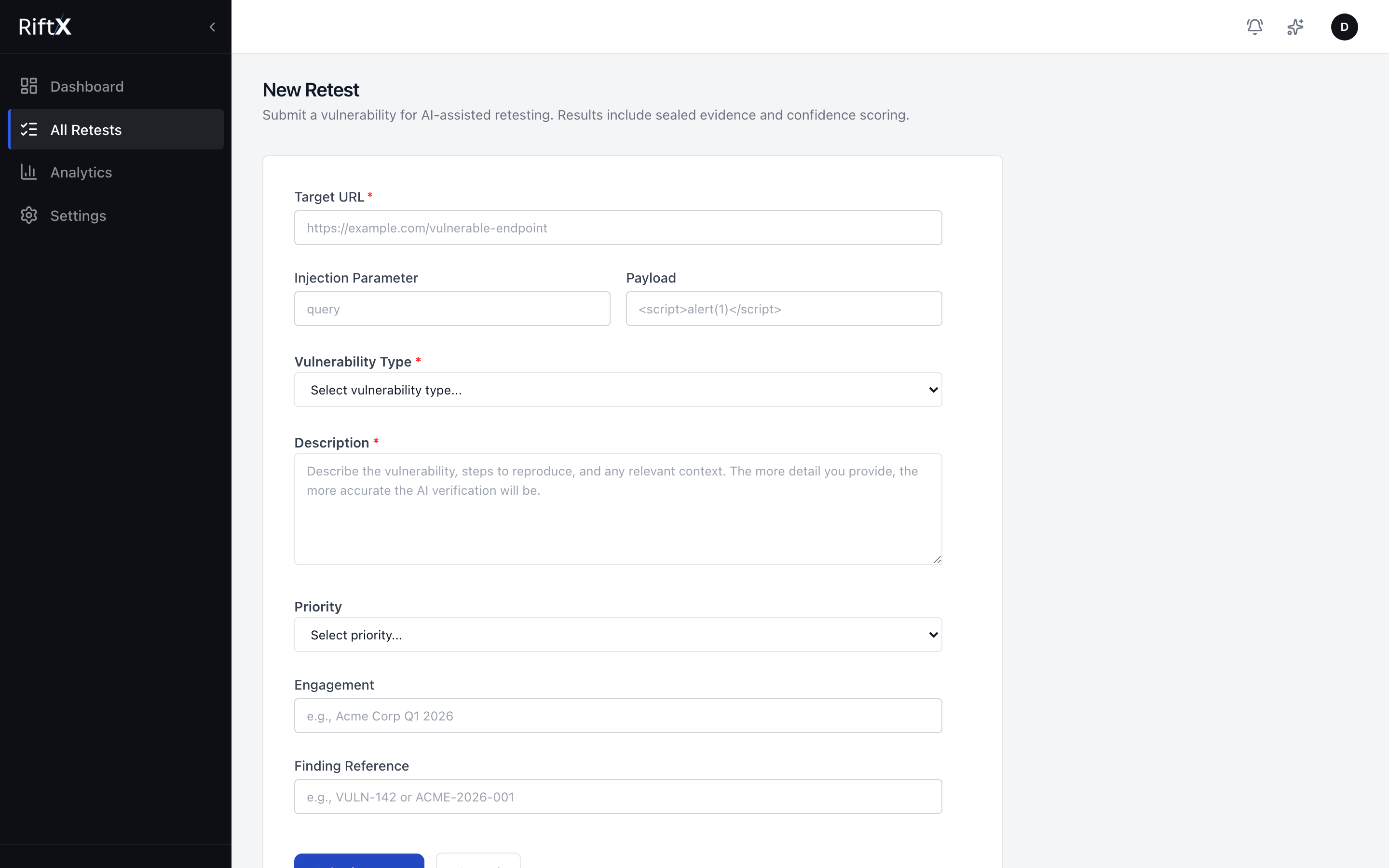
Steps-to-reproduce, target, and workflow context enter the system in a way pentesters can read quickly and trust.
average per retest
evidence bundle attached
returned instead of a guess
Reproduction steps are the control surface
Payload is optional. Reproduction steps are the primary input, because that is how retesting actually starts in a consultancy.
The system works from what the pentester actually did, not from a perfect proof-of-concept that may never have been documented in the ticket.
{
"target_url": "https://example.com/search",
"vulnerability_type": "reflected_xss",
"description": "XSS in search parameter",
"steps_to_reproduce": [
"Navigate to /search",
"Enter payload in the q parameter",
"Observe alert box fires"
]
}RiftX reads the steps, identifies the likely vulnerability profile, and chooses a verification strategy.
The goal is not to invent a new attack path. It is to replay the reported path faithfully and capture evidence cleanly.
reported finding → replay → verify → seal evidence
The ReAct verification loop
Observe, detect, act, and validate. Deterministic signals fire first, and the loop keeps itself honest by checking state change after every step.
Observe
The agent captures DOM state, console output, network activity, and browser events before it commits to the next action.
Detect
Deterministic signal detectors evaluate the observation first. Dialogs, timing, response artifacts, and headers are checked before any LLM fallback.
Act
Based on the current phase, the agent chooses the next browser action: click, type, submit, wait, or verify.
Validate
Each action is checked for state change. If the page stalls or diverges, the loop adapts instead of guessing.
Verification artifact in motion
Observation captured
Signal sweep running
Browser action selected
State change validated
Evidence is part of the verdict, not an afterthought
Every verification bundle is designed to be reviewed by a human pentester after the agent finishes.
HTTP Traces
Full archive of every request and response
Screen Recording
Recording of the browser execution
HTML Report
Request/response visualization for your report
Integrity Seal
HMAC-SHA256-sealed evidence integrity
less manual work per retest
average time to verdict
reproduction accuracy
Exactly three outcomes
No soft maybes and no vague probability language. The agent either verifies, cannot verify, or stops honestly at a review boundary.
The reported vulnerability could not be reproduced. The fix appears effective.
Vulnerability confirmed with reproducible evidence. The original issue persists.
Execution hit a safety or fidelity boundary, so the agent stayed honest.
When RiftX cannot verify, it returns Needs Review. It does not guess to create a prettier report.
Built-in safety limits
Every retest runs inside hard boundaries. If any limit is hit, the system terminates rather than improvising.
API-first from submission to result
Submit retests programmatically, track state cleanly, and attach the evidence bundle back into the rest of your tooling.
curl -X POST https://api.riftx.io/jobs \
-H "Cookie: token=vt_live_..." \
-H "Content-Type: application/json" \
-d '{
"target_url": "https://example.com/search",
"vulnerability_type": "reflected_xss",
"steps_to_reproduce": [
"Navigate to /search",
"Enter payload in the q parameter",
"Observe alert box fires"
]
}'{
"job_id": "job_7f3a2b1c",
"status": "queued"
}Fits the tools your team already uses
RiftX receives reported findings and returns verified verdicts through the systems your team already relies on.
Vulnerability Reported
Jira / Burp Suite / API
RiftX Receives
Goal setting & planning
Browser Executes
Real Playwright verification
Verdict Returned
Evidence → back to your tools
REST API
Submit retests, poll results, and retrieve evidence programmatically. JSON in, JSON out.
Webhooks
Get notified in real time when a verdict is ready. Push results to any endpoint.
Jira
Auto-create verified finding tickets with HAR, GIF, and confidence score attached.
Slack
Team notifications when verifications complete. Verdict, confidence, and link to evidence.
Burp Suite
Right-click a finding in Burp and send it to RiftX for autonomous verification.
ServiceNow
Enterprise ITSM ticket creation with full evidence chain for compliance workflows.
Get your pentesters out of the retesting loop
Your pentesters should be finding vulnerabilities and writing reports, not manually retesting the same XSS for the third time this month.